Industrial Internet of Things (IIoT) – up-to-date solutions and keys you need to know


Over the past few years, a multitude of industries have been implementing the Industrial Internet of things technology, yet it has become a real catch for the manufacturing industry. As for tech’s merits, the most substantial ones are raising efficiency, high-quality items delivering on one side, and resource managing on the other. What is more, IIoT is a key to improving resilience to crises, especially topical during the COVID-19 pandemic. The system provides companies with the cost-efficiency of operations and maintains their business continuity, protecting enterprises against emergencies. In addition, ensuring workers’ safety at industrial facilities is another critical advantage. Not surprisingly, Meticulous Research claims that the IIot market is to increase steadily and will reach $263 billion by 2027.
As the name implies, IIoT aims to enhance industrial and manufacturing processes using actuators and smart machines. Therefore businesses can benefit from data produced and analyzed by engines in real-time because the risk of human errors declines considerably. Actuators and sensors help companies detect pressing issues or inefficiencies, which is crucial for time and money-savings. Thanks to the system, compilating data is available in Business Intelligence as well as in Artificial Intelligence.
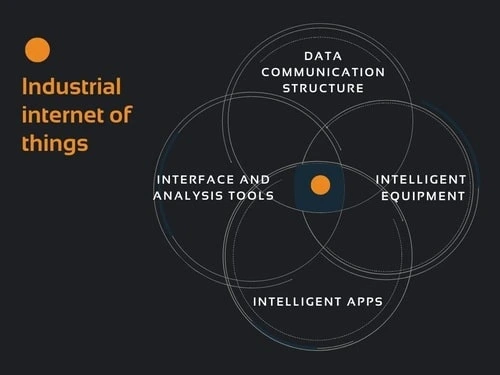
Basic IIoT connects intelligent machines linked to databases through the networks. Although several types of tech are able to satisfy your business needs, a typical Industrial IoT includes the following features:
Well, that’s no wonder that the system’s adopters focus on strengthening software and firmware security for cyberattacks prevention. So which follow-ups should take place to safeguard your IIoT?
1. Pay attention to the IIoT network segmentation.
2. Encrypt device communication.
3. Introduce two-factor authentication.
4. Control user access to information and smart gadgets.
5. Filter both outbound and inbound traffic.
6. Integrate a real-time security monitoring system.
7. Install software patches and updates on a regular basis.

Most vitally, assessing IIoT is the starting point for avoiding threats, particularly penetration testing. Besides, it is crucial to build the capacity of the workers to help them recognize the cyber-threats promptly. Regular and compulsory training is one of the surest ways to protect IIoT in the industrial environment. Another necessity is conducting risk analysis to detect architectures’ weaknesses, shortcomings in APIs, enabling devices, and protocols.
Ultimately, you should be ready for an emergency, so a few corporate actions are worth compiling. Which steps do you have to map out? Check out the bullet points below.
The primary function associated with IIoT technology is definitely connectivity. Meanwhile, the diversity and multitasking of the system help users to deal with various challenges. Each type of system has its own set of tools, pros and cons, risks, and possibilities. That is why you can select that very IIoT Development option to meet your requirements fully. So let’s consider all the features of cutting-edge solutions.
1. LPWAN
Low Power Wide Area Networks connect all kinds of IIoT sensors, facilitating many apps, starting from environmental monitoring to facility management. They also provide assets tracing, consumables evaluating, and occupancy detection. These systems are designed for supporting large-scale networks of booming industrial and commercial enterprises. However, as LPWANs are inclined to send a small amount of data at a slower rate, this option will be appealing for not time-sensitive targets. If your company is determined to achieve too high bandwidth, explore other kinds of Custom Solutions Development.
2. Cellular (3G/4G/5G)
This one perfectly suits fleet management in logistics, transportation, and ensuring car connection because of its ubiquitous cellular nature and high bandwidth.

Without any difficulties, systems support numerous voice calls and streaming apps. What is more, this option is expected to be a godsend for augmented reality and autonomous vehicles. The only drawback of cellular is relatively high operational expenses and energy consumption. But bear in mind that the system won’t be a solution for IIoT apps, powered by battery-operated networks.
3. Bluetooth and BLE
Bluetooth was initially created for point-to-point and point-to-multipoint data exchanging. Wireless connection development, optimized for power requirements, is now beneficial for small-scale applications. BLE-enabled gadgets, for their part, are often utilized for creating the so-called smartphone hub. It helps to transfer essential data to the cloud. The ample examples of BLE integration can be found in Smart Home, fitness, and medical devices.
4. Zigbee and Other Mesh Protocols
Zigbee and comparable mesh protocols are essential for HVAC control protocols, smart lighting, security, and energy management.
They also appeal to those industries that don’t need complex network management and setup. Unlike the LPWAN solution, Zigbee is less power-efficient. On the other hand, the system ensures much higher data rates.
Our company provides clients with the best software development services. PNN Soft has 20 years of experience in creating highly efficient solutions, but we’ve spent decades honing our skills to deliver the newest technologies. Our team is also specialized in creating IIoT, and we know what kind of system will spell success for your enterprise.
So if you are searching for an IoT device manufacturer, fill in the form below.