Mobile security in 2021. Best practices for iOS/Android
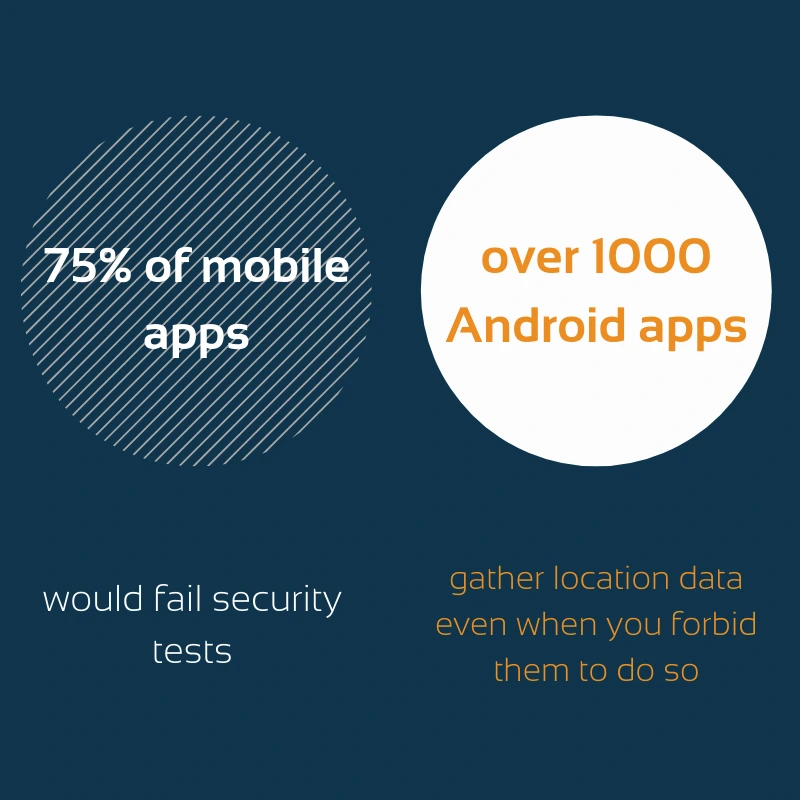
With the era of public/private 5G, cloud, and remote working, mobile data protection has taken on new relevance. Security leaders and experienced developers contend with a growing variety of challenges, as cybercriminals are targeting mobile users more actively than ever before. In addition, security researchers claim that both Android and iOS apps are still unsafe. According to Gartner, 75% of mobile applications would fail security tests. At the same time, over 1000 Android apps gather location information, even when you forbid them to do so.
In this context, it becomes quite obvious that both users and developers should do their best to prevent the invasion of privacy and other cyber threats. There’s nothing like working in tandem and joining efforts in applying security standards. Customers can start by setting a strong passcode, using random passwords, and disabling ad tracking.
Today we want to share other simple but effective ways to decrease the likelihood of security issues. We’ve divided this post into two parts to give you iPhone and Android essential privacy and security tips. Let’s talk about effective practices for users first, and then dwell on security tips for developers.
If you are determined to turn your mobile phone into a more secure device, then keep up reading. The same principles are paramount when it comes to protecting your tablet from data leaks.
As the name implies, two-factor authentication provides your Apple account with a second layer of security. So when you log in from a new device, you need to enter a one-time-use code and a password. And hence, even if someone has your password, it won’t be enough to assess your account without a computer or phone.
Because otherwise, your iPhone may display personal data or certain features without requiring your passcode. Take a look at the features available on the lock screen in the Allow Access When Locked area. For instance, you may disable Return Missed Calls, Notification Center, or Reply with Message features.
Numerous apps require your location to track where you are shopping, while users tend to click through notifications mindlessly. Open the Privacy area and make sure that location services are set to Never or While Using. As for weather apps and other applications that need approximate location only, disabling Precise Location is a good idea. If you use mobile apps for business and seek extra security, you may take full advantage of our IT security services. Just click on the link.
You can find three sections under the App Privacy area in the App Store: data not linked to you (motion sensor data), information related to your identity, and data used to track you. Inside these sections, there are 14 kinds of data apps may gather about you. The simplest way to check out privacy is to open the App Store, tap your icon, and find My purchases setting. It’s better to use the app with relatively short labels. Also, pay particular attention to applications with data used to track you. Don’t hesitate to contact mobile development experts and get more information.
With the help of this feature, your account can be hidden behind a random email address that forwards to your real one. All you have to do is consider creating an account with your Apple ID.
How to make your IOS application secure without great effort?

It’s time to discuss how to protect your personal information when using Android devices.
As a rule, leading antivirus companies have their own Android-malware applications, such as Avast, Norton, or Kaspersky. You can get a robust AV app for free, namely Lookout and TrustGo.
Nowadays, there’s no point in keeping extra-sensitive data on your tablet or mobile phone. Download applications that store data behind double encryption and protection. File Hide Expert and mSecure are at the top of our list.
Numerous applications on the Google Play market enable owners to wipe or lock their gadgets in case of theft. Cerberus and Avast Mobile Security react to a text command or you can utilize them via the web interface.
Such cheeky goldmines are sometimes related to a ‘middleman’ attack when the third party acquires personal details, including your credit card number.
This tip will be useful for those who are thinking about creating an on-premise app and hiring Android developers. You should know that all the documents you keep on internal storage are available only for your app. Try to avoid both MODE_WORLD_READABLE and MODE_WORLD_WRITEABLE for your IPC files. These modes fail to provide control of data format as well as limit data access to particular apps.
Here we’ve put together a list of security features for Android developers:

PNN Soft has been delivering programming products for 20 years, and we hone our skills to put our ideas into the newest solutions and services. We also provide our clients with IT consulting services. In this process, special attention is paid to security.
We are focused on achieving an in-depth understanding of individual companies’ features and needs. That is why our clients prefer long-term cooperation.
PNN Soft gives priority to Agile, Scrum, and RAD methodologies to interact with clients effectively, satisfy customers’ needs and obtain more flexibility. Our Agile teams of experts include software developers, GUI designers, testers, technical writers, and managers.
If you are searching for reliable outsourcing mobile development or IT consulting, contact us by filling in the form below.